永續議題
Supplier management policies and related compliance specifications
The Company has a supplier management policy in place, and regards suppliers as
important partners of the Company’s operations. In promoting corporate social responsibility, the Company considers the participation of the entire supply chain, besides maintaining quality and delivery, we also drive the supply chain to value human rights, protection of environment, health and safety, strengthen suppliers’ Environmental, Social and Governance (ESG) management, including green environmental protection, labor human rights and ethics, health and safety, risk management and ethics, and prohibition of minerals from conflict areas, etc., to jointly establish a sustainable supply chain.
1. Supplier CSR risk management: AOT has developed the “Business Code of Conduct for Suppliers’ CSR” in accordance with Code of Conduct – Responsible Business Alliance,RBA In the procurement contract, AOT’s suppliers must pass the supplier evaluation and sign and commit to comply requirements. Assess the social, economic, and environmental risks of existing suppliers, and adopt audit control for suppliers assessed as high-risk, and supervise and correct actual and potential obvious negative deficiencies.
2. Supplier quality management: For the quality management of key materials, new suppliers are evaluated based on quality, cost, delivery time, technical ability, and selection is made for suitable suppliers for cooperation. The current key material suppliers are evaluated based on the non-performing delivery rate, service quality, and procurement delivery deadline. If they are not up to the standard, we would provide guidance and counseling. If there is still no effective improvement, the supplier will be removed from the qualified supplier list.
3. Procurement risk diversification
(1) Material shortage risk management: The Company coordinates the material preparation mechanism with suppliers and establishes safety stocks according to the preparation time required for each material to ensure a smooth supply chain. To avoid the risk of material shortage or having only a single supplier, we will select two or more qualified suppliers according to the material evaluation mechanism for product development, and select new qualified suppliers based on product development needs through selection and evaluation process to ensure the smooth supply of materials.
(2) Local procurement: AOT production is concentrated in Taiwan and China. The supply chain mainly includes suppliers and related contractors of machine equipment, key spare parts such as LEDs, printed circuit boards, electronic materials, lighting modules, and materials, energy resources, and transportation. In order to shorten the time required for material preparation and accelerate the development time of new products, the Company actively implements localization of materials, which can also reduce costs and carbon emissions generated during the transportation process, and create a triple-win situation for the AOT, suppliers, and the local economy.
The comprehensive management of suppliers
1. On supplier management for critical materials, quality meetings are held with suppliers regularly to review related issues and make continuous improvements, in order to meet quality improvement requirements.
2. On supplier management system verification, we would visit important suppliers as planned every year and conduct on-site audits. Once defects are discovered, the suppliers will be required to propose appropriate improvement plans to meet AOT expectations.
3. Assessments for critical materials are made on a monthly basis based on the non-performing delivery rate, service quality, and procurement delivery deadline. Provide evaluation results to suppliers to urge them to make improvements.
Supplier management policies and related compliance specifications
1. Procurement: The suppliers that pass the material evaluation must have the ISO9001& ISO14001 environmental certification and provide the quality guarantee and the environmental restricted substances testing consent.
2. Certification: Quality verification includes QSA and QPA.
(1) Suppliers with two scores >= 80% are qualified
(2) Suppliers with any item with a score of less than 80% cannot supply goods until the defects are corrected
(3) Performance and monitoring: In order to achieve stable quality and continuous improvement, monthly performance evaluation and annual audit (same certification content as above) are conducted.
3. Supplier sustainability assessment:
The Company conducts its Sustainability Index evaluation and selection of suppliers of raw materials. The annual evaluation of qualified suppliers in 2025 conforms to 100% of supply chain management mechanisms.
Communication Channels and Response Methods
Contact Window: Procurement Department
Phone: +886-3-5976988
Email: scm@aot.com.tw
Quality Policy
The HSF quality policy is based on principles suitable for the operation of the AOT organization and complies with HSF quality management system requirements and commitments to continuous improvement. The HSF quality policy serves as a framework for establishing and reviewing HSF quality objectives, facilitating internal communication and understanding within the organization, and ensuring regular reviews of its ongoing appropriateness. Control of hazardous substances must comply with relevant HSF regulations and customer requirements to achieve HSF product quality and continuous improvement.
Quality Objectives
Each department establishes relevant performance indicators and HSF quality objectives based on the HSF quality policy and the company’s strategic direction within the implemented HSF quality management system processes. The achievement of HSF quality objectives is reviewed through regular management review meetings. Control of hazardous substances must comply with related regulations and customer requirements to achieve HSF product quality. We are committed to implementing and continuously improving the IATF 16949:2016 and HSF quality management system. We are dedicated to maintaining and achieving the HSF quality policy and meeting various requirements while continuously improving the HSF quality management system.
Conflict Minerals Management
AOT is committed to not using conflict minerals and is dedicated to conducting thorough investigations of the supply chain to ensure that metals such as Tin (Sn), Tantalum (Ta), Tungsten (W), Gold (Au), and Cobalt (Co) are not sourced from mines controlled by armed groups in the Democratic Republic of Congo and its neighboring countries.
Important Statement
AOT does not procure or use conflict minerals from the Democratic Republic of Congo and its surrounding countries and regions.
Suppliers are required not to procure or use conflict metals produced in conflict regions and must sign a commitment not to use conflict minerals.
Suppliers are required to communicate this requirement to their upstream suppliers.
Information Security Management Policy
AOT is committed to safeguarding the confidentiality, integrity, availability, and legality of its information assets. Understanding that robust information security is vital to maintaining a competitive advantage and ensuring organizational longevity, AOT is dedicated to implementing and maintaining effective information security management practices. This includes continuously enhancing our capabilities to protect sensitive information, increasing employee awareness, and fostering vigilance concerning information security. We strive to prevent unauthorized use, disclosure, alteration, or loss of information due to human error, deliberate sabotage, or natural disasters. Our goal is to protect the interests of the company, its shareholders, employees, customers, and suppliers.
The Company’s information security management policy was submitted to the board of directors in November 11, 2025.
Information Security Management Objectives
- Conduct Annual Information Security Training: Facilitate comprehensive information security training sessions at least once per year and periodically disseminate and promote information security updates to reinforce employee awareness and accountability regarding information security responsibilities.
- Perform Annual Internal Audits: Execute internal audits of information security protocols annually to ensure adherence to established security practices and verify effective implementation.
- Implement Annual Disaster Recovery Drills: Conduct disaster recovery exercises annually to ensure familiarity with recovery procedures and mitigate potential operational disruptions.
- Ensure High System Availability: Guarantee that critical operational systems achieve a minimum availability rate of 99.7% following planned maintenance activities each year.
- Prevent Data Leakage Incidents: Maintain a record of no incidents involving the leakage of critical business data to safeguard the interests of the company, its clients, and its stakeholders.
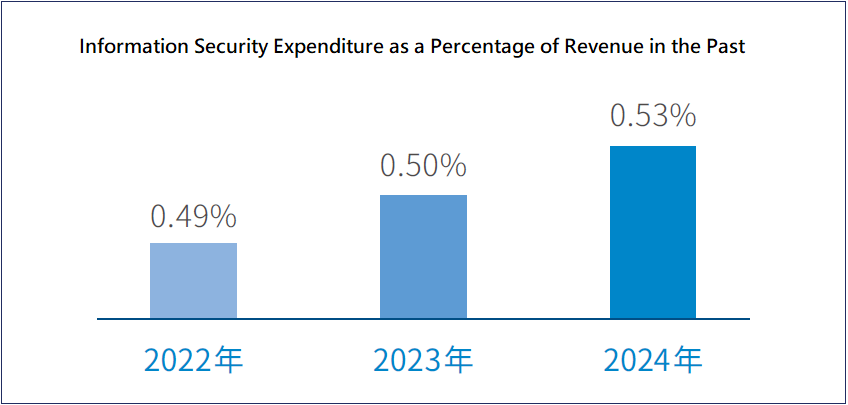
- Information Security Expenses Account for More Than 0.4% of Revenue (ESG Sustainability Report)
- 2023:0.50%、2024:0.53%
Information Security Risk Management Framework
- The dedicated information security team is tasked with the oversight and execution of the company’s information security policies, the promotion of information security awareness, and the enhancement of employee understanding regarding security responsibilities. This team is responsible for regularly reporting information security outcomes to the Chief Information Security Officer (CISO) and the General Manager. Furthermore, the CISO will deliver an annual report to the Board of Directors on information security governance matters, including the evaluation and verification of the effectiveness of internal controls over information operations. This framework aims to ensure the confidentiality, integrity, and availability of information by establishing a “Continuous Improvement of Information Security Resilience” management structure to mitigate risks associated with unauthorized access, damage, or leakage.
- To advance ESG (Environmental, Social, and Governance) sustainability, comply with regulatory requirements and corporate governance assessments, and enhance enterprise information risk management and data protection, the company is committed to investing in the upgrading and implementation of information security technologies and solutions. The company has implemented the ISO/IEC 27001:2022 Information Security Management System and was successfully certified by SGS on November 26, 2025. SGS has recommended the company for registration with UKAS as an organization compliant with ISO/IEC 27001:2022. The scope of certification covers information security management activities, including the operation and maintenance of the Enterprise Resource Planning (ERP) system, network and data center maintenance and management, and is aligned with the Statement of Applicability, version V02.
Information Security Risk Control
- Evolving Cyber Threats: With the constant evolution of cyberattack techniques, information systems face significant challenges in fully mitigating disruptive attacks from external parties. These attacks may involve methods such as phishing emails, spear-phishing, brute-force attacks, and the deployment of malicious software within the company’s internal network to cause damage or data theft. Destructive attacks could lead to interruptions in production and operations, while data theft attacks may result in the exposure of critical operational data or personal information of employees and customers. The company is proactively planning and implementing information security measures, continuously improving the security environment and infrastructure to mitigate information security risks.
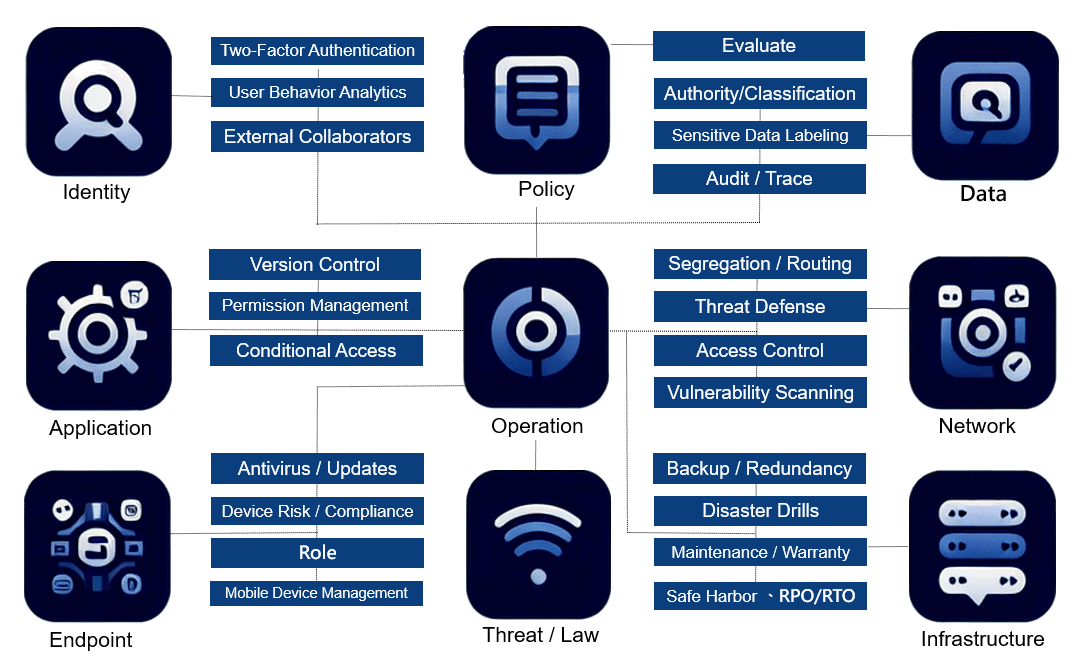
- Management Framework: Employing a Zero Trust Architecture, the management framework encompasses policies and procedures across various domains, including organizational responsibilities, asset management, access control, physical security, personnel security, document management, communications and operations management, system development and maintenance, business continuity management, incident management, and regulatory compliance.
- Technical Measures: Implementing a suite of technical controls, including network firewalls, backup and redundancy systems, antivirus software, regular operating system updates, email security systems, virtual private network (VPN) management, security monitoring systems, and vulnerability scanning tools.
- Audit and Testing: Conducting a comprehensive audit of the company’s information security management system in the first half of the year, and scheduling emergency response plans and disaster recovery drills in the latter half. Annual reviews are conducted to assess information security operations, risk controls, and incident remediation efforts to manage and reduce information security risks.
- The information security management policy and achievements were reported to the board of directors in November 11 2025.
- Social engineering drills and penetration testing were conducted in 2025.
- Joined the Taiwan National Cyber Security Alliance (Taiwan CERT/CSIRT Alliance) in July 2024, effectively utilizing cyber intelligence through information sharing to enhance self-defense capabilities in cybersecurity.
- The company began planning for the ISO/IEC 27001 Information Security Management System in October 2024, and was successfully certified by SGS on November 26, 2025. SGS has also recommended the company for registration with UKAS as an organization compliant with ISO/IEC 27001:2022, in order to strengthen its information security management framework.
Continuous Improvement of Information Security Resilience Management Framework
Privacy Protection
- The Company maintains the confidentiality of personal information related to all business partners (including suppliers, customers, consumers, and employees), and has established management mechanisms and relevant codes of conduct, including: “Information Security Management Guidelines,” “Document Encryption System,” “IT Control Procedures,” “Internal Personal Data Protection Guidelines,” “Work Rules,” and training standards. These are designed to ensure customer rights, privacy protection, and fulfillment of product safety commitments, as well as to safeguard the information security requirements of customers, employees, and suppliers. Confidentiality practices meet the reasonable expectations of business partners. When collecting, storing, processing, transmitting, and sharing personal information, we strictly comply with the Personal Data Protection Act and other regulations related to privacy and data security.
- The “Internal Corporate Personal Data Protection Management Regulations” are formulated by the General Administration Office to ensure that the company complies with the statutory requirements of the Personal Data Protection Act, and to reasonably utilize and protect personal data.The scope of personal data protection includes information such as name, date of birth, national ID number, passport number, physical features, fingerprints, marital status, family details, education, occupation, medical records, healthcare, genetic information, sexual life, health check results, criminal records, contact information, financial status, social activities, and other data that can directly or indirectly identify an individual.
- General Administration Office: Serves as the contact point for employee-related personal data complaints, inquiries, and incident reporting. Also assists in organizing personal data protection training.
- IT Department: Responsible for establishing information security systems to protect personal data from hacking, alteration, damage, loss, or leakage. It strengthens security controls and manages cybersecurity risk prevention and incident response mechanisms.
- Legal Department: Provides legal consultation and support for incident handling, and assists in personal data protection training.
- Department Heads: Supervise data users to ensure compliance with relevant regulations.
- Audit Unit: Conducts irregular audits of the implementation of personal data protection management in accordance with internal audit procedures. It ensures compliance, provides recommendations for improvements, and may report serious deficiencies to the Board of Directors.
In 2025, the company held personal data protection training, with a total of 498 participants and 498 training hours completed.
Product Safety and Marketing Labeling
The Company complies with relevant regulations and international standards (e.g., ISO 9001 Quality Management System and ISO 14001 Environmental Management System). It strictly adheres to the “Green Product Management Operating System,” the RoHS Directive restricting hazardous substances, and REACH regulations concerning Substances of Very High Concern (SVHC).
The Company also values customer feedback. In addition to routine client visits, a customer service email is provided on the Company website. A dedicated stakeholder section has been established, with responsible personnel from the Sales Department handling customer inquiries, complaints, or suggestions. Upholding the principle of integrity, the Company ensures appropriate responses and feedback to protect customer rights.
Communication channels and response methods
Contact Window: Sales Department
Telephone: +886-3-5976988
Email: sales@aot.com.tw